CYNTHETIC CYBERSECURITY SERVICES
- IT Security
- Security Assessments Vulnerability Improvement Physical | Detection | Response Server Configuration
- Network Configuration
- Policy & Procedure Development Security Awareness
- Gap Analysis
- Support
- PC / Servers / Network
- Anti-Virus / Spam
- Filtering
- Securing Email
- Surveillance Systems
- High Value Businesses Encryption
- Endpoint Security
- Education & Seminars
Security team coming available.
Core practice areas of expertise include Physical Infrastructure, Security Solutions, and Network Monitoring & Management.
IT Security task team in coming available with specific skills and knowledge to assist with improvement, controls and compliance of computer and network security. This team has a well versed knowledge computer security, and has specific skills to improve posture across network, server, computer and mobile devices. If you have specific needs for compliance in finance or health care this team can assist with assessment, documentation and hands on controls improvement. Team has specific NIST, HIPAA and FISMA experience protecting PII (Personal Identifying Information). This team has specific experience implementing the following:
Effective Backup Scenarios
Two Factor Login & Security Controls
Endpoint & Email Encryption
Network Security Controls
End User Guidance and Education
Contingency & Disaster Recovery Planning and Documentation
Compliance Documentation
Securing Technical Environments
Profile:
IT Security Subject Matter Expert understanding, guiding and developing compliance. Strong communications skills both written and verbal. Experience working with C level executive teams as well and technical teams to achieve objectives. Hands on experience employing security tasks on network, server, desktop and mobile devices. Extensive understanding of NIST, HIPAA and FISMA rules, standards and guidelines.
These technologies consist of;
VMWare Technologies: vSphere 5.1, ESXi
Server Administration
Windows Operating systems
Cisco Devices – PIX (515), ASAs (5510), Switches (3750, 3560), Catalyst Switches (5500) Routers (3800, 3900)
Networking Technologies – RIPV2, OSPF, STP, Port security, ACLs, VTP, NAT, PAT
Brocade 48 port Fiber Switches
Storage Area Networks (SANS) – EMC,Dell Compellent, & EquaLogic
Windows Server technologies – WSUS, WDS, SCCM
Backup technologies – Symantec System Recovery 2011 & Netbackup
Enterprise Virus & Anti spyware solutions – McAfee epolicy orchestrator suite (HIPS, Policy Auditor, DLP, ACCM, Anti virus & Anti Spyware)
Served as a liaison to the governing body for development, execution and review of all configuration baselines, ensure compliance, monitor and identify trends, and create remediation actions as necessary. Experience working in data sources including systems such as Windows, Linux, VMWare, networking, and telecommunications to collect and analyze information. Security experience to capture baseline, event log, patching and compliance data and leveraged for sustainment of compliance and information technology security initiatives. Provided the enterprise-wide coordination for these actions. Ensured that sustainment activities are coordinated and executed according to a pre-determined schedule, as well as worked to ensure vast amount of information is turned into actionable data for vulnerability and compliance remediation.
Prioritize threat bulletins
Create Change Orders/action items for patch needs
Create compliance reports
Security program Development
Audits
Compliance
Review & strategy
Assessments
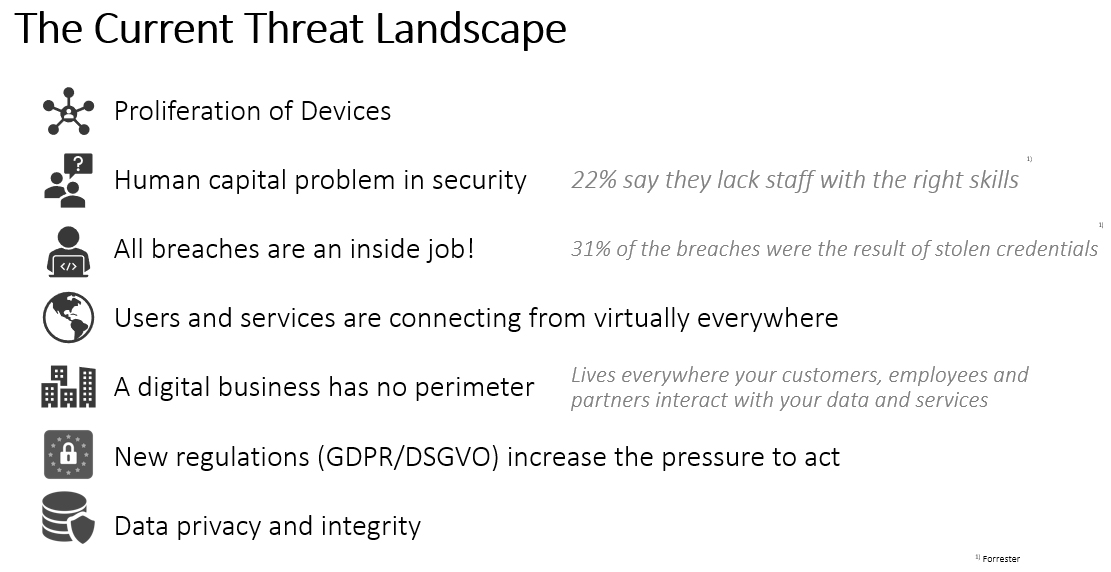
We help identify gaps in existing capabilities across the people, processes, applications, data, technology and physical facilities across your organization.
We help prioritize security initiatives and investments for optimal return.
We help simplify and speed the planning and execution of a straight forward security program.
We help you reach a desired security posture.
Contact us for a consultation.
(720) 649-5882
sales@cyntheticsystems.com
NAICS code 511210 – cybersecurity software (encryption)
NAICS codes 517110, 518111, 518210, 54151, and 54121 – design and development of network security systems
Approaches for Federal Agencies to Use the Cybersecurity Framework
NISTIR 8170
Recommended Security Controls for Federal Information Systems
System Security Plan (SSP)
Field Security Services – Standard Operating Procedures
TESTIMONIALS
The team at Cynthetic is amazing. The amount of thought and breadth of knowledge has been instrumental to my business. I recommend doing the discovery call. I hadn’t even hired them yet – and they gave me straight forward ideas that I could implement myself.
BITEHEIST


Fast, supportive, thoughtful. Amy and her team covered all the details needed to get my employees working from home. They have instilled a new confidence in our ability to use tech.
BARSTOCK IO
I never thought about IT like these guys do. When I asked Amy “What am I going to do with my office closing?” – she promptly said “Get your VOIP phones on your cell and computer, make sure you set up teams with the manager, make sure your email is accessible, think about your patients and communicate.”
Denver Dental Spa